How to protect PHI & PII on AWS and HIPAA Compliance
The Challenge
HIPPA (Health Insurance Portability and Accountability Act) regulations were made to keep the privacy of the healthcare industry while using the latest technologies available in the market. Healthcare uses both Personally Identifiable Information (PII) and Protected Health Information (PHI).
First of all, we need to isolate the network and restrict access to it, not expose any server to the outside world, and use public services protected with Firewalls (Like a WAF on an ELB or CloudFront), so no one could access the data.
Second, we need to make sure all environments are isolated within themselves (Dev can't access Prod), and the connection is private to each of them so that no data breaches will occur. We want to be aware of who will access and what they can do in our environment. All sessions need to be recorded, access is restricted and monitored, even if unauthorized personnel try to get to data, we will know about it.
Finally, all the data must be encrypted (in both EBS and S3) and backed up as much as possible so no data will ever be lost.
The Solution Architecture:
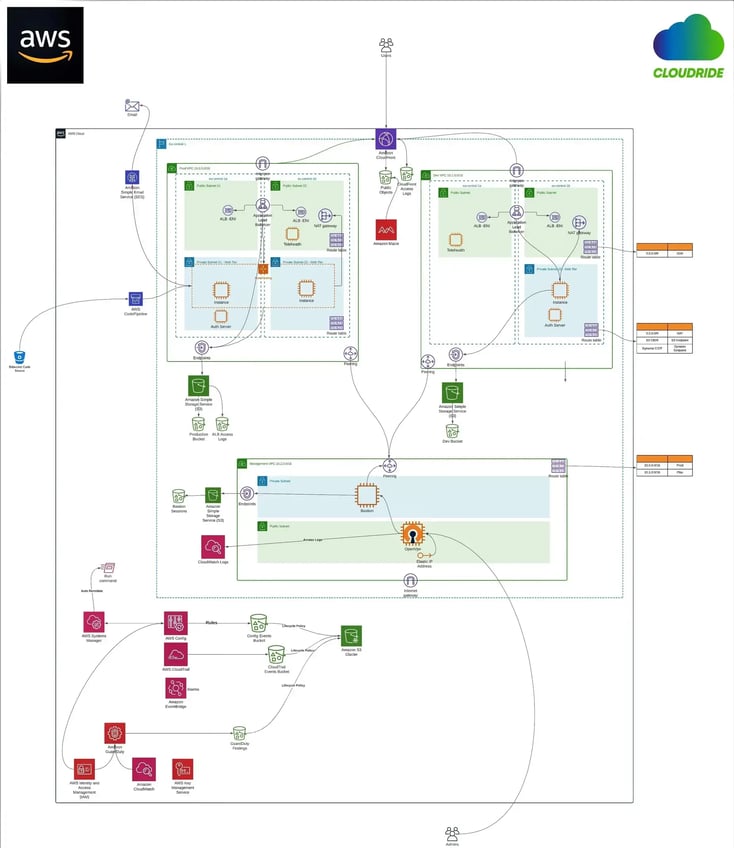
The Cloudride Solution:
We took a small startup and decoupled their application and networks. It went from an architecture of servers with Public IP's that can be accessed from everywhere to a private, isolated network. All servers are not accessible from the internet, only via an Application Load Balancer and CloudFront distribution with AWS WAF integrated on them.
In order for Administrators and Developers to access a server, they need a VPN connection and go through a recorded Bastion Server that logs every action they do. It is impossible to connect from Dev to Prod; all connections are private using VPC Peering. Even when accessing public services such as S3, we use a private connection called VPC Endpoint.
In terms of the data itself, we use SSL certificates to authenticate and encrypt the data in transit and use Encrypted EBS volumes and S3 buckets to keep the data encrypted at rest. We were using Config rules to prevent creating unencrypted volumes.
Regarding backups, all backups are managed in AWS Backup vault and Amazon Glacier, which holds the server's backups and the event trailing in the account.
As for monitoring, all Actions in the account are monitored (API actions using CloudTrail, Changes to Security rules using Config, ALB, and CloudFront write logs to an S3 Bucket).
If it’s all a bit too much, no worries, we’re here to help you out!
Even if you harden all your environment, someone can still make changes and use unapproved non-compliant resources. So maintain the Hardening using policies and Config rules to make sure this won’t happen.
Use the native backup services and define backups on a schedule that will let you roll back and go back before a major event happens. If you can restore all the environments from backups, you can sleep better at night.